TRUEFORT PRODUCT
Zero Trust Microsegmentation for Cyber Resilience
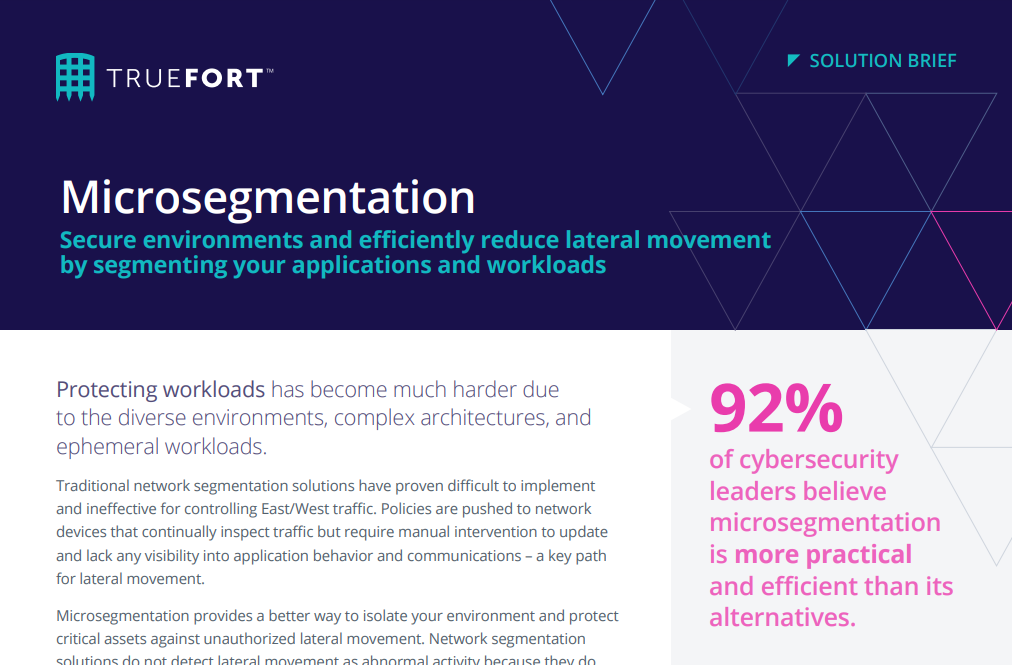
Protecting workloads has become much harder due to the diverse environments, complex architectures, and dynamic application changes. This creates an overly trusted environment that existing infrastructure tools weren’t created to understand. TrueFort provides intelligent microsegmentation to prevent access to business-critical assets.
TRUEFORT PRODUCT
Zero Trust Microsegmentation for Cyber Resilience
Protecting workloads has become much harder due to the diverse environments, complex architectures, and dynamic application changes. This creates an overly trusted environment that existing infrastructure tools weren’t created to understand. TrueFort provides intelligent microsegmentation to prevent access to business-critical assets.
Next-gen firewalls and IP-based segmentation prevent very little
- Understanding attack surface – Threats from the outside and compromised insiders cannot be stopped from moving laterally by existing network security tools.
- Discovering and mapping applications – Identifying a trusted baseline of expected workload and account activity in operating environments is impossible from security alerts alone.
- Excessive entitlements – Excessive entitlements occur for users and machines, and are rarely adjusted or revoked when reducing risk.
- Ensuring optimal operations – Eliminating high-risk activity across workloads is challenging without sacrificing application performance.
Understanding behavior across all workloads is mandatory
Deep asset discovery
Identify all of the workloads running your applications to view an optimized environment
Powerful behavioral understanding
Use machine learning to understand workload behavior within applications. Adapt a trusted baseline for application changes and take control of unusual behaviors
Granular application visibility
Automate comprehensive mapping of complex application relationships and data flows, including the process, identity, and location
Control over lateral movement
Enforce automated blocking for network connections, service account usage, or command line execution outside the norm for any microsegment
The path to
microsegmentation
The negative impacts of successful attacks require a preventative approach via zero trust, with microsegmentation uniquely positioned to ensure that the impacts of an incident are limited.
To foster broader adoption, solutions supporting microsegmentation must be easy to use and straightforward to deploy, generating accurate, automated policy recommendations.
of organizations are currently using microsegmentation.
of organizations plan to use microsegmentation in the next 12-24 months.
GET THE GUIDE
Emphasizing Prevention with Microsegmentation
FAQ
Microsegmentation is a security approach which helps administrators implement the principle of least privilege and Zero Trust for individual workloads. Instead of applying one policy to an entire network or data center, microsegmentation allows security to manage traffic between workloads or applications within a network. Security policies deny user requests by default unless they present the right credentials for the specific data they’re trying to access.
Microsegmentation may be used to isolate workloads in development, testing, and production, manage connections to specific applications, limit application visibility by user, user group, or tier, and apply fine-grained controls to specific software services and processes.
Microsegmentation plays an important role in reducing an organization’s attack surface because it gives security teams control over what lateral movement to permit in any environment. With this control, experts can monitor lateral movement against predefined security policies or against a model of expected application behavior, which improves the speed of detection, response, and remediation.
Microsegmentation makes it possible to implement granular control of network communications, credential usage, and approved behavior to help organizations minimize the impact of a cyber security incident, and solutions with automated application discovery will simplify security management even as networks grow increasingly complex.
Microsegmentation doesn’t require a new architecture for implementation. Security teams can deploy an agent-based solution which leverages software existing agents on the workload to isolate individual hosts and containers. Solutions can apply security policies based on physical and virtual devices, including load-balancers, switches, or software-defined networks. Some cloud service providers also offer microsegmentation capabilities.
Organizations will typically deploy both agent-based and network device models to handle all environments, including public or private cloud and on-premises networks. Solutions will use the visibility microsegmentation provides and data analytics to develop a model of normal network behavior against which anomalous events stand out for fast detection and response.
Resources